It’s not every day that we conduct an interview which is rudely interrupted by the resolution of the entire premise of the interview, but it does happen occasionally. It happened once when we interviewed a hacktivist who had to hang up because the nurse was taking him to rehab, where he’d been put as a result of his hacking. It happened again yesterday, when we interviewed the primary journalist/researcher behind Dark.fail, a domain which they’d lost control of, and which they regained while in conversation with me. Us. Whatever.
[Hello, Officer Friendly]
Dark.fail is a website that attempts to review the reliability of various darknet sites, many of them drug-related, but many not. It is maintained by a team of fewer than a dozen activists and researchers.
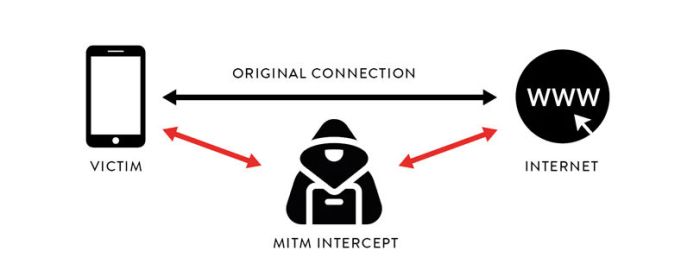
On April 29th, a hacker or hackers seized control of the domain and switched it to point to a dupe of the site, which then directed uses not to pre-approved, recommended safe sites but to 68 different phishing sites, which is a classic “man in the middle” attack. They then tracked all the login details for those sites which users supplied, and presumably can then use those to make purchases on their own or sell the credentials.
If you used the site over that hijacked period you should assume your credentials got stolen, and you should change your password/passphrases and check your account balances.
Here is the public statement from Dark.fail:
If you visited sites listed on the clearnet domain "dark.fail" between April 29th through May 5th 2021 you were phished and should rotate all credentials immediately! ... A phisher stole our domain and operated it for four days in a highly sophisticated attack that bypassed all security protocols we had in place, including 2FA. The attacker sent a fake German court order to Njalla's partner Tucows and convinced them to transfer our domain to Namecheap. They then listed 68 phishing replicas of real sites on our domain, stealing an untold amount of cryptocurrency from these sites' researchers and users. They also hijacked DarknetLive.com. It took Namecheap four days to transfer our domain back to us. Every site listed on the domain "dark.fail" from April 29th through May 5th 2021 was a man-in-the-middle phishing proxy. Each site looked real but instead shared all user activity with the attacker, including passwords and messages. Cryptocurrency addresses displayed on these sites were rewritten to addresses controlled by the phisher, intercepting many people's money.
Dark.fail has publicly claimed that losses sustained by those using the hijacked site exceed a quarter-million Euros over those four days.
Here is the edited-for-clarity transcript of that interview. And yes, it’s good to get back to work after what, five years away? Welcome back.
So, let’s start with the big picture stuff: can you tell me about the mission of your website?
Dark.fail educates researchers on how to authenticate information in the “darknet,” (Tor hidden services) and performs our owni independent research on darknet site
There is so much misinformation out there about what really exists on the darknet. Reliably finding and interviewing sources can be next to impossible with how much phishing goes on, how many fake sites exist.
We educate people on how to authenticate information by verifying PGP signatures, and we maintain a list of sites we find interesting to our research that are hosted on Tor.
What makes a site worth listing?
Our primary platform for publishing has been Twitter thus far, the website itself is just our list of authenticated, accurate sites we find interesting. We’re working to launch a blog very soon and move our publishing there.
When it comes to cryptomarkets, we look at the number of familiar vendors selling on each site, the overall site transaction volume, and the site’s reputation among users in darknet forums. It’s common for admins to completely burn their identities and start fresh when launching a new site, so it’s really hard to tell which cryptomarket is built by an experienced team.
We look closely at the code that is visible to end users, and pay close attention to the security practices implemented by the market. In our experience the admins that invest the energy into coding something from scratch, using the community’s latest best practices – those admins tend to be the most serious and interesting to pay attention to.
Are you compensated in any way by the cryptomarkets or any of the sites you list or review?
Our only source of revenue is through the donation address displayed on our website, we do not know the identity of any of our donors.
We have been very cautious to follow the law. In 2018 American law enforcement arrested DeepDotWeb, the only major source of news covering the darknet. They included affiliate links in their URLs and accepted payments from darknet admins in exchange for listing. Since day one of our launch we have remained committed to not making the mistake of being drawn into the criminal world that we research as outsiders.
Dark.fail has been a hobby for a long time. It has long been our dream to work on it full time. We are in the process of building out the legal infrastructure to facilitate that at last. We will keep the donation approach as an option for revenue. Our goal is to follow a subscription model for access to premium content and tools useful to researchers.
How does the legal concept of journalistic privilege apply to a listing of approved markets? Governments have been attacking journalistic privilege for decades, eroding it.
We believe strongly that mass surveillance of global citizens will only increase. Studying the fringe methods that criminals use to hide their servers is of utmost importance to preserving freedom of speech. We’re heading towards a world where technologies like Tor will be the only way to access an internet that is free.
Law enforcement’s takedown of DeepDotWeb’s content was an outrage. Arresting the individuals involved in laundering criminal proceeds made sense. But deleting a news organization’s entire publishing history was an affront to journalistic freedoms. I can’t believe there hasn’t been more outrage about this. When a news site is seized, an archive of its content should be published.
As a cybersecurity researcher myself, even I have been phished many times when trying to find which markets are most the relevant. Many people study the global drug trade, and the tracing of cryptocurrency. It was near impossible to avoid getting phished in the scope of my research in 2018 when Dark.fail launched. This was a driving motivation in the development of the site. It’s useful to me, so it must be useful to other researchers out there.
Indeed, but it’s only as useful as your reputation, and building a rep in a world of anonymity of pseudonymity is hard. Which is why we are talking. How many journalists have used your site?
We currently get around two million uniques per month on our clearnet mirror. We do not track metrics on our darknet mirror.
Twitter is my primary publishing platform. My posts there have been cited by many articles. In terms of my listing of sites, and how many researchers have found it useful, that’s not an easily quantifiable metric since I respect people’s privacy by not logging. Researching cryptomarkets carries a lot of legal risk in most jurisdictions. Rasmus Munksgard has an excellent book about this. The last thing I want to do is increase the legal risk of those using my resource.
Any journalist that has sources in the criminal underworld is a target for law enforcement to flip. We do not engage in conspiracies. We commit no crimes in our jurisdictions. But LE would love to use our trust to deceive others, just like the phisher just did. Dark.fail’s reputation is strong. This is from our steadfast commitment to being honest. A rare trait in a world of anonymous cybercriminals and undercover feds. I think our honesty angers people who lie for a living.
We’ve pulled off trust by being consistent over time. I am grateful that the vast majority of the darknet research community still trusts us after our failures, like the recent phishing domain takeover.
The 250k Euros lost (over four days) is a big number. How did you arrive at that figure?
I maintain several cryptomarket admins as sources. A few were willing to share figures of how much they saw their revenue decrease. This combined with my knowledge of this space led to the estimate. I am in the process of trying to identify the attacker. A possible criminal investigation is also being opened, not sure of the jurisdiction but I think Germany would be the place to prosecute it since my domain was stolen using a forged German court order.
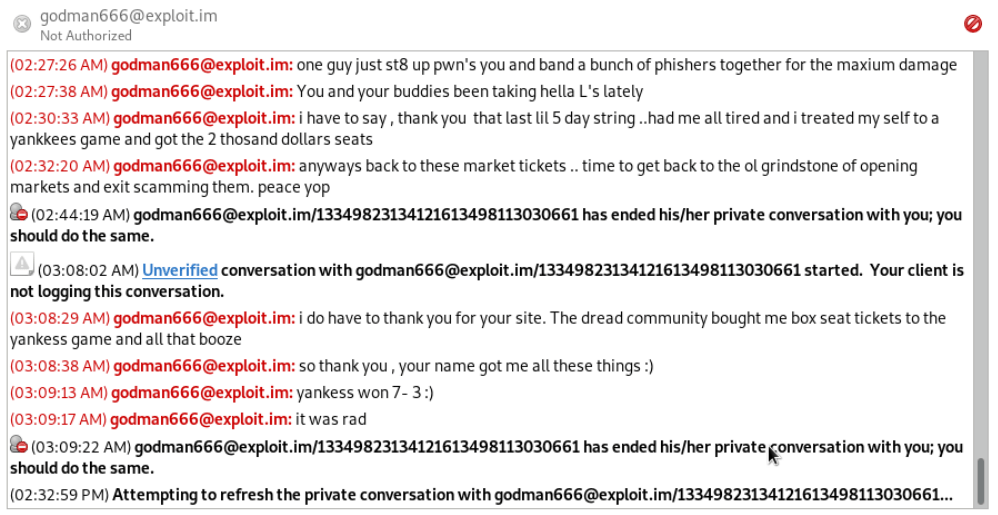
Notorious phisher and admin exit scammer Godman666 has claimed responsibility for the attack but he may just be wanting the attention.
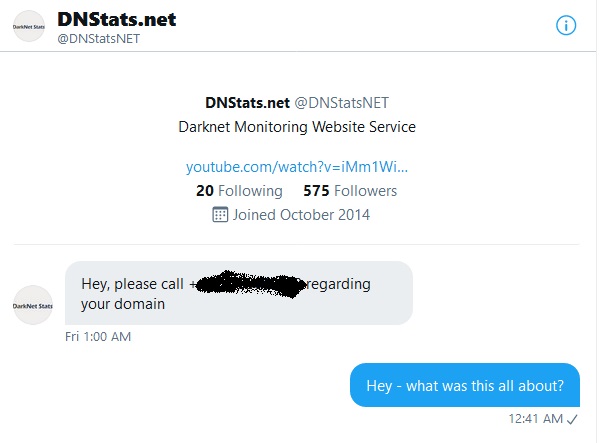
DNStats used to be a reputable source of authenticated links but was purchased by a phisher years back. DNStats sent me a cryptic message on twitter during the attack so I also suspect them.
Ultimately many people want to bring us down.
Few sites are trustworthy sources of darknet information. Besides Dark.fail, I only trust Darknetlive and Oniontree.org. Darknetlive was also hijacked by the phisher, a testament to their trustworthiness and the value that they provide.
Law enforcement I’m sure also wants to bring us down. Many of our donation addresses were flagged by blockchain analysis company Chainalysis. This placed us in a strange, nearly “crypto-unbanked” situation earlier this year. Transfers from our Bitcoin donation address to a major exchange were frozen, we have no easy recourse. So we switched to only accepting donations in Monero.
Do you think the domain switch/phishing is state sponsored? And if so, which nation? It would allow the FBI to nab a LOT of people.
No. This was a highly coordinated phishing attack. If it were state sponsored they would have used a proper court order. Or I would be under arrest and coerced into doing it myself.
To learn the OPSEC of a market admin, and to teach those skills to journalists and activists, from day one I have assumed the same threat model as a market admin. I assume that I need to hide my identity just as intensely as any cryptomarket admin. This has taught me a ton about the incredible challenges of maintaining anonymity in our ad-tech, mass-surveilled world.
If our phishing takeover were state sponsored it would need to be from a state that does not have many checks and balances to protect its citizens’ civil liberties.
The same anonymity that protects us also allows unscrupulous researchers and cops to bend ethical boundaries without ever disclosing their identity.
It’s interesting from an ethical perspective that anonymity or pseudonymity may become a mark of reliability. Because your “normie” self is too surveilled to be independent.
I’ll claim that as my quote please. :) Completely agree.
Have Namecheap replied to you at all? Do you think this is an attempt to force you to identify yourself, so you can prove you own the domain?
It’s immensely difficult to dispute anything without revealing my true identity. I’ve pulled it off but wow.
No customer service reps know what PGP is. My PGP key is who I am. Darknet researchers get that, I can sign a message and post it anywhere and set the record straight any time. But in a Namecheap support ticket? Forget it. Njalla claims they submitted over 20 abuse tickets to Namecheap.I want to sue Namecheap. But I can’t without doxxing myself. You can really beat up an anon a lot easier than a normal person. And in most jurisdictions an anonymous person cannot anonymously retain an attorney.
So you ultimately have to decide when and to whom to doxx yourself.
This was the most apalling Namecheap update IMO:
They were racing to reset as many passwords registered to my email hello@dark.fail as they could. They weren’t able to get past 2FA anywhere that supported it.
I was able to keep tweeting using Buffer until the attacker figured that out.
Lesson learned: don’t register critical accounts to an email hosted at your domain.
I could not access my Twitter at all during the attack. They did not access my Twitter, they just locked me out of it. They did not get past Twitter’s 2FA but were able to partially reset the password.
My Buffer account was the only way I could tweet until they reset that password somehow, again they were unable to get past 2FA.These resets might have just been account locks until I was able to both solve 2FA and prove ownership of my email.
Where does it stand right now? Are there other accounts connected to that domain? LinkedIn, Keybase, whatever?
I’ve regained access to everything that was registered to “hello@dark.fail”. I have 2FA enabled everywhere so the fallout was minimal. Companies should really require 2FA to reset a password. That would have stopped this.
Where do you go from here? What’s your next step to get that domain back?
[Darkdotfail then goes dark for ten nerve-wracking minutes. The last time this happened in a chat somebody got v&]
So I got the domain back! Njalla is unparalleled in service.
WAIT WHAT? Okay, walk me through how that happened.
So when it happened I raised hell everywhere. Njalla support ticket, Namecheap abuse ticket. Namecheap hosted the phisher’s list of 68 phishing sites on my domain for four days straight. Njalla quickly got to the bottom of the situation. I did not realize that they were a Tucows reseller, this is my fault for not digging deeper into my supply chain. So I pay Njalla because I hold their security in high regard, but they go use Tucows and pay them with fiat currency of course.
Tucows received a faked court order from a German court, did not verify it, and respected a faked gag order not to tell Njalla or myself of what was happening. Tucows transferred the domain to another account at Tucows, then to Namecheap into the phisher’s hands.
Njalla relentlessly pursued this hijacking. They met with Tucows, they persistently followed up with Namecheap. It’s clear that Njalla is not asleep at the wheel. They take their reputation as seriously as I do. I will continue to strongly recommend Njalla to other activists.
Thankfully they [the hackers] only got control of the domain name. They did not access any servers or code. They pointed the domain name at other hosting providers that they controlled, which were running their code, a clone of my site that pointed to 68 phishing proxies.
That’s what was so highly coordinated – not only did they use the most aggressive domain takeover approach I’ve ever heard of – but they also launched 68 fake versions of darknet sites, proxies which logged all user traffic as it passed through to the real site the user thought they were visiting.
That must have taken quite a lot of work. Was this organized crime perhaps? Have you heard of takeovers like this before?
These “man-in-the-middle phishing proxies” (MITM proxies) dynamically replace any cryptocurrency addresses with addresses owned by the phisher. So when a user logs into an account using their username and password, the attacker not only steals their credentials, but also shows them the real website. It’s really hard to tell that you’re on a phishing site when it’s a proxy. And of course, any time you go to buy something, the cryptocurrency address shown by the site you think you’re visiting is overwritten by the phisher’s address.
Godman666 is a prolific phisher and has claimed responsibility for the attack, but DNStats.net is also implicated [by the contact attempt screenshotted above]. It’s possible multiple phishers ganged up on me.
So, that’s where it stands today. Someone went to the trouble of creating 68 plausible dupes for existing sites, plus a dupe for Dark.fail itself, and fake documents plausible enough to wrest control of the URL away from Tucows and Njalla, who are normally pretty sharp companies.
If you used Dark.fail to get to a marketplace during the hijacking period, you should assume your credentials got stolen, and you need to check your wallet and change your credentials immediately. Things are back to normal there, but an elaborate hack like this requires a substantial investment of time and/or resources, so you should assume it will happen again to another site.
Categories: Attack, Cryptosphere, Dark Web, Hackers, Journalists, Man in the Middle, Media
Reblogged this on raincoaster and commented:
And, after five years away recovering from The Accident, The Cryptosphere is back! With an exclusive interview with darkweb researcher DarkDotFail on how his site was stolen by hackers in a man-in-the-middle attack. And the attack was thwarted and reversed DURING the interview!
LikeLike